What is the Internet of Things (IoT) and why does it matter in everyday life?
Connected technology is no longer limited to phones and computers. It’s increasingly built into everyday objects, from smart speakers and household devices to transport systems, connected medical devices, and public infrastructure. As these systems become more common, they start to influence how environments function and how routine tasks are carried out.
This guide explains what the Internet of Things (IoT) is, how it works, and why it has become an integral part of modern life. It also outlines key challenges and limitations, providing context for why device security is an important consideration for everyday appliances.
What is IoT?
IoT is a network of physical objects (things like thermostats, fitness trackers, smart speakers, factory machines, and cars) equipped with sensors, processors, and connectivity hardware that enable them to collect data and communicate with other systems, often without direct human input.
Each device or gateway is typically assigned a unique identifier (such as an IP address) and may exchange data over the internet, through local networks, or via gateways using wired or wireless connections.
According to the National Institute of Standards and Technology (NIST), an IoT device is computing equipment with at least one transducer, such as a sensor or actuator, and at least one network interface. In practice, IoT systems combine sensing, computing, communication, and sometimes actuation, enabling them to detect changes, process data, communicate with other systems, and, in some cases, take action in the physical world, such as adjusting a valve or turning on a light.
General-purpose computers like laptops and smartphones aren't usually counted as IoT, even though they're connected. They're treated as the interfaces people use to interact with IoT systems, rather than IoT devices themselves.
According to IoT Analytics, connected IoT devices were expected to reach about 21.1 billion by the end of 2025, with the total estimated to reach 39 billion by 2030 and more than 50 billion by 2035.
How does the Internet of Things work?
An IoT system is built around a data pipeline: devices capture information from their environment, transmit it across a network, and feed it to platforms that turn it into decisions or automated actions.
This involves several components working in sequence: sensors and devices that gather data, networks that carry it, and cloud platforms or local processors that interpret it and coordinate responses.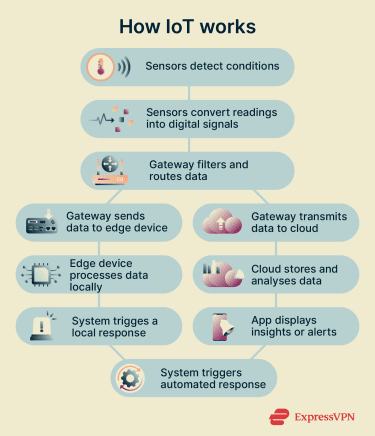
A common simplified way to describe IoT systems is the three-layer model: perception, network, and application. The perception layer collects data from the physical world, the network layer carries that data, and the application layer turns it into something useful. More detailed IoT models may add processing, middleware, business, or security layers.
Also read: IoT infrastructure: Components, architecture, and best practices.
Sensors and connected devices
Sensors are the “eyes and ears” of an IoT system. They detect physical conditions (temperature, motion, vibration, humidity, location) and convert them into digital data.
A typical IoT device contains a microcontroller (a small onboard computer), connectivity hardware such as a radio, modem, or wired network interface, and a power source, such as a battery, energy-harvesting component, or mains power. The quality of these components, especially the sensor itself, directly affects how reliably the system can detect and respond to events.
Networks and data flow
Once a device collects data, it needs a way to send it onward. The right connectivity technology depends on the use case, specifically, how far the data needs to travel, how much of it there is, and how much power the device can afford to use.
Short-range technologies like Bluetooth and Zigbee (a low-power wireless protocol common in smart home devices) work well within a single room or building. Wi-Fi covers larger indoor spaces and, according to IoT Analytics, is currently the largest IoT connectivity technology, accounting for about 32% of global IoT connections.
Cellular networks, such as 4G and 5G, are used when devices need to communicate over long distances or while moving: think vehicle tracking or remote field sensors. For battery-powered devices that only need to send small amounts of data over large areas, low-power wide-area networks (LPWANs), such as Long-range wide area network (LoRaWAN) and cellular IoT options such as narrowband IoT (NB-IoT), provide energy-efficient connectivity, usually at lower data speeds than broadband cellular connections.
Also read: What are IoT networks? A complete guide.
Cloud platforms and automation
Once data reaches a gateway or connected platform, the system can process it locally on an edge device or send it to the cloud.
Edge computing processes data close to where it's generated, reducing network traffic, improving response time, and keeping some data on-site for privacy or reliability. This is useful when a connected vehicle or industrial control system needs to respond quickly, or when a factory sensor can't afford to wait for a round trip to a remote server.
Cloud platforms take over for the heavier workloads: long-term storage, analytics across large fleets of devices, and machine-learning models that spot patterns at scale. They also feed dashboards and trigger automated actions across the wider system.
People interact with all of this through a web page or mobile app, where they can monitor what's happening and adjust settings. This is what makes IoT practical day-to-day: instead of requiring constant human attention, devices can act on their own, like a smart fridge adjusting its cooling when its sensors detect warmer interior temperatures, or a connected security camera alerting your phone the moment it detects motion.
Learn more: IoT cloud security: Threats and best practices.
Why is IoT important: Key benefits and impact
IoT matters because it makes systems, from a bedroom thermostat to a factory floor, more responsive, efficient, and informed. Its impact plays out differently depending on the context, but the underlying principle is the same: devices that once operated in isolation can now sense, share data, and act on it automatically.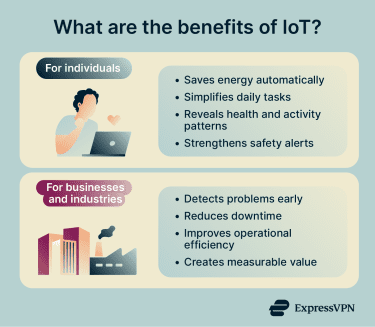
For individuals
- Can reduce energy waste: IoT systems, such as smart thermostats and building controls, can reduce unnecessary energy use by matching system activity to real-time conditions, for example, running heating or cooling only when and where it’s needed.
- Reduces friction in daily routines: Connected systems can handle repetitive tasks automatically, adjusting settings based on time, occupancy, or habit without requiring manual input each time.
- Turns data into personal insight: Continuous sensing turns everyday measurements into recognizable patterns over time, such as correlations between physical activity and sleep quality that a single snapshot would miss.
- Boosts safety: Connected devices can coordinate alerts across an entire space rather than signaling in isolation, giving people more time and context to respond to a potential danger.
For businesses and industries
In industrial settings, sensor data can flag early signs of equipment stress before a breakdown occurs. According to McKinsey (a strategy and management consulting firm), predictive maintenance typically reduces machine downtime by 30–50% and extends machine life by 20–40%.
The productivity gains, cost savings, and new services that IoT enables add up considerably at scale. Another McKinsey report estimates that IoT could unlock between $5.5 trillion and $12.6 trillion in global economic value by 2030, with factories accounting for the largest share and human health accounting for a major portion.
Common examples of IoT in everyday life
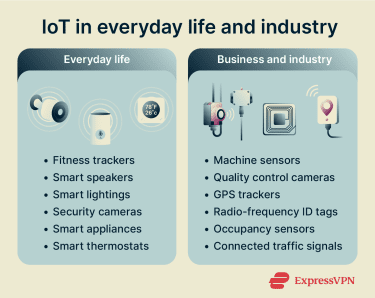
The following are some of the most widely used consumer IoT devices today:
- Wearable fitness trackers: Smartwatches and fitness bands use sensors to monitor heart rate, sleep stages, and daily activity. More advanced models may measure blood oxygen levels, record an electrocardiogram (ECG), or detect signs of irregular heart rhythms, depending on the device and region. Data can sync to a mobile app, where it can be reviewed over time or, in some cases, shared with a healthcare provider.
- Voice assistants and smart speakers: Smart speakers respond to voice commands to play music, answer questions, set reminders, and control other connected devices in the home. They can also act as a voice control point, and some models serve as smart home hubs for connected devices.
- Smart lighting systems: Connected lighting uses occupancy sensors and scheduling to adjust brightness based on whether a room is in use and the time of day. Lights can be controlled remotely through an app, grouped into zones, and integrated with voice assistants or other smart home devices.
- Home security cameras and sensor networks: IoT cameras and motion sensors provide home monitoring, with footage stored locally, in the cloud, or both, depending on the system. Some systems include AI-powered detection that can distinguish among people, animals, vehicles, packages, and other activity types, helping reduce unnecessary motion alerts.
- Smart appliances: Connected refrigerators, washing machines, and dishwashers use sensors to track usage patterns, report faults, and notify users when consumables are running low. Some models allow remote start and stop, and can provide usage or energy information through a companion app.
- Smart thermostats: Many connected thermostats use schedules, occupancy detection, geofencing, or learning features to avoid heating or cooling an empty house. Users can monitor and adjust settings remotely, and some systems provide energy usage reports.
How the Internet of Things is used in business and industry
Businesses and industries use IoT to move from reactive operations (fixing problems after they occur) to data-driven operations, where decisions are informed by continuous, near-real-time, or event-based data.
Smart manufacturing
Connected factory floors deploy sensors across production equipment to measure operating parameters, such as vibration, temperature, pressure, torque, and cycle times. This creates a continuous picture of machine health, allowing maintenance teams to inspect or service equipment based on actual condition rather than fixed schedules.
IoT also supports inline quality control. Smart cameras and connected sensors positioned at key checkpoints can perform dimensional inspections and monitor variables such as weld current or cavity pressure in real time, triggering automated rejects before a defective part advances further down the line.
Asset-tracking tags on tools, materials, and finished goods give operators a live view of inventory locations across the factory floor. Energy-monitoring systems can also track consumption across individual machines and production lines, making it possible to identify inefficiencies that would otherwise go unnoticed.
Also read: IoT device management: Complete guide.
Connected transport and logistics
Fleet operators use IoT to monitor vehicles. Onboard sensors report location via GPS, along with engine diagnostics, fuel levels, and driver behavior data. Fleet managers can view operations from a single dashboard, reroute vehicles in response to traffic or delays, and identify vehicles approaching scheduled maintenance thresholds.
In logistics, IoT extends that visibility to the goods themselves. Radio Frequency Identification (RFID) tags (small tags that use electromagnetic signals to identify and track objects without requiring direct line of sight) help identify items as they pass checkpoints, while GPS trackers can report shipment location over longer distances when power and network coverage are available.
For temperature-sensitive goods such as pharmaceuticals or fresh food, environmental sensors and data loggers can record conditions throughout transit, helping show whether specified temperature ranges were maintained.
Smart buildings and cities
In commercial buildings, IoT systems connect heating, ventilation, and air conditioning (HVAC), lighting, and access control into a single managed environment. Occupancy sensors feed data to building management systems that adjust heating, cooling, and lighting room by room based on whether spaces are actually in use, rather than running on fixed schedules.
At the city scale, IoT can support public infrastructure. For example, adaptive traffic systems can use sensor data to adjust signal timing based on traffic conditions rather than relying only on fixed cycles.
Connected streetlights equipped with motion sensors can dim when an area is empty and restore full brightness when pedestrians or vehicles are detected. Air quality monitoring networks can provide authorities with continuous, granular data on pollution levels across different parts of a city, supporting both public alerts, research, and longer-term environmental policy.
Also read: What is IIoT and why its security matters more than ever.
What are the biggest risks and challenges of IoT?
IoT's scale and diversity make it uniquely difficult to secure. Unlike laptops or smartphones that receive regular software updates and are actively overseen by users, IoT devices are often small, low-cost, and designed to operate unattended for years. That combination creates a distinct set of risks, spanning cybersecurity, privacy, physical security, and regulation.
Learn more: Check out our ultimate guide to IoT device security.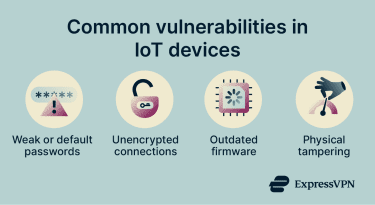
- Device security and botnets: Many IoT devices ship with weak default credentials, limited processing power for security software, and infrequent firmware updates, making them attractive targets for attackers. Compromised devices can be recruited into botnets (networks of hijacked devices used to launch attacks at scale). In March 2026, U.S. authorities and international partners disrupted infrastructure used by the Aisuru, KimWolf, JackSkid, and Mossad IoT botnets, which had compromised more than 3 million devices, including DVRs, webcams, and Wi-Fi routers, and were used to carry out distributed denial-of-service (DDoS) attacks.
- Vulnerability disclosure and transparency: A 2026 report by Copper Horse and the IoT Security Foundation found that only about 40% of global consumer IoT manufacturers reviewed provided a mechanism for reporting vulnerabilities. Without transparent reporting, vulnerabilities can go unpatched for extended periods, leaving users exposed.
- Weak or missing data protection: Some IoT devices may transmit data without adequate encryption, while others protect the content but still expose metadata such as destination servers or connection times. This makes data protection in transit and at rest an important part of IoT security.
- Insecure defaults and attack vectors: Many IoT devices ship with weak default credentials and outdated firmware. Their accessibility makes tampering easier and could theoretically allow malware to form botnets and launch large‑scale attacks.
- Broad attack surface: IoT devices may expose web dashboards, mobile apps, cloud accounts, APIs, Bluetooth, Wi-Fi, or other services. Each interface can become an entry point if it's poorly configured, outdated, or weakly protected.
- Regulatory compliance: The EU Cyber Resilience Act (CRA) introduces mandatory cybersecurity requirements for many products sold in the EU. Reporting obligations for actively exploited vulnerabilities and severe incidents take effect from September 2026, while most other obligations take effect from December 2027. For device manufacturers operating across multiple markets, navigating overlapping regulatory frameworks like this adds significant complexity and cost
- Physical tampering: Unlike servers locked in a data center, many IoT devices are physically accessible: a thermostat in a hallway, a sensor on a factory floor, a camera mounted outdoors. Physical access can allow someone to manipulate a device directly, potentially causing false readings, device failure, or, in the worst case, a route into the wider network it sits on.
Protect your IoT devices with a virtual private network (VPN)
Most IoT devices can’t run a VPN app on their own, but installing a VPN on a compatible router can route the internet traffic of connected devices through an encrypted VPN tunnel. This can add privacy protection for smart home devices, security cameras, and connected appliances, but it should be used alongside strong passwords, firmware updates, network segmentation, and secure device settings.
Also read: How to secure your smart home from cyber threats and attacks.
What does the future of IoT look like?
IoT's growth is expected to continue well into the next decade. GSMA Intelligence (the global mobile operator data, analysis, and research platform) forecasts that global IoT connections will reach 40.8 billion by 2030 and 52.9 billion by 2035, with enterprise applications rising from 65% of total IoT connections in 2030 to 69% by 2035.
GSMA Intelligence also forecasts that the global IoT market will reach $2 trillion in revenues by 2030, roughly doubling from $1 trillion in 2024. The firm identifies enterprise IoT as the largest driver of that growth.
Several technologies and design priorities will shape how that growth plays out. AI is increasingly being integrated into IoT platforms to process sensor data at scale, identify patterns, and trigger automated responses that would be impractical to manage manually.
5G, with its low-latency and high-device-density capabilities, can make demanding IoT deployments more practical, including autonomous vehicles communicating with road infrastructure, large-scale industrial automation, and dense citywide sensor networks that need to support very large numbers of connected devices in a given area.
As deployments expand in scale and complexity, edge computing is expected to become more central to IoT infrastructure design. Processing data closer to where it is generated (rather than routing everything to a distant cloud) becomes increasingly important as the volume of IoT data grows and response time requirements tighten.
Security is also evolving from an afterthought into a design requirement. The EU Agency for Cybersecurity (ENISA) calls for more proactive preparation for emerging threats, while the CRA introduces mandatory cybersecurity requirements for many connected products sold in the EU. Together, these shifts mean future IoT devices will increasingly be expected to address security from the start, including connectivity, data handling, updates, and lifecycle management.
Also read: How IoT is transforming public safety and emergency response. However, some functionality, such as remote monitoring, updates, and large‑scale analytics, may still require cloud services.
FAQ: Common questions about IoT
How is IoT different from artificial intelligence?
Does the Internet of Things (IoT) always need an internet connection?
How much data do Internet of Things (IoT) devices collect?
Can IoT devices work without the cloud?
What should you check before buying an Internet of Things (IoT) device?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN











Comments
Great
If you have a separate GPS from your cell phone, can you be tracked through it. It would not have a sign up or address connected to it. There are also 2 versions of GPS. There are ones with Bluetooth, that can work with unwired backup cameras and cell phone speaker transmission. There are those without bluetooth. What can you tell me?
Last moment to run away from them. Delete ALL unnecessary data, especially PHONE, ADRESS, KIDS, health, origin, most of photos, what you love/ hate, where you travelled, what you bought, said, where you protested. States, banks, corporations are thieves,spies and executioners who work for slaveowner cults & they pretend its not happening. Delete FB, IG, WApp, iG, X and others if possible, soo, turn Windows t W8 or earlier, sabotage tracking, get alt OS. The more we give, the more they take.