Celebrities’ and influencers’ private communications exposed in stalkerware data breach

Recently I discovered a non-password-protected and publicly accessible database that contained 86,859 images of what looked like screenshots of a user’s device, apparently related to stalkware targeting one specific person. It logged activity and chat conversations from Facebook, WhatsApp, Instagram, and TikTok accounts.
The messages revealed private communications with models, influencers, and celebrities, as well as what appeared to be intimate, romantic exchanges and images that were not meant to be public. The database was named after a well-known service that provides spyware promoted as monitoring software. It appeared to have been uploaded by an individual targeting another person. Based on our findings, the exposed database didn't belong to the software provider it was named after.
Upon further review of the exposed files, I identified that the victim of the spyware is a prominent European celebrity, entrepreneur, and media personality. The images capture chat conversations with influencers that have millions of followers, as well as with friends, family, business associates, and others. For privacy reasons, I cannot identify the victim or others whose private communications were unknowingly exposed. The screen captures exposed highly sensitive information, including phone numbers, emails, pictures of documents such as invoices, receipts, identifications, and more.
In most situations when data is exposed, a company or organization is responsible for those records, and I can notify them with a responsible disclosure notice to secure the data and block public access. In this case, it appears that the individual who managed the malicious software created the database to store and access these images. In the process, they misconfigured the access controls to allow anyone with an internet connection to access these potentially sensitive images and conversations. Because installing stalkerware on a device is a potential criminal act, I notified law enforcement, and using phone numbers identified in the screen captures, I notified the victim.
This image shows a collage of captured video calls, highlighting how the stalkerware captured much more than chat messages and pictures.
This image is a collage of how the screen captures appeared in the database that included private images, chats, and other activities.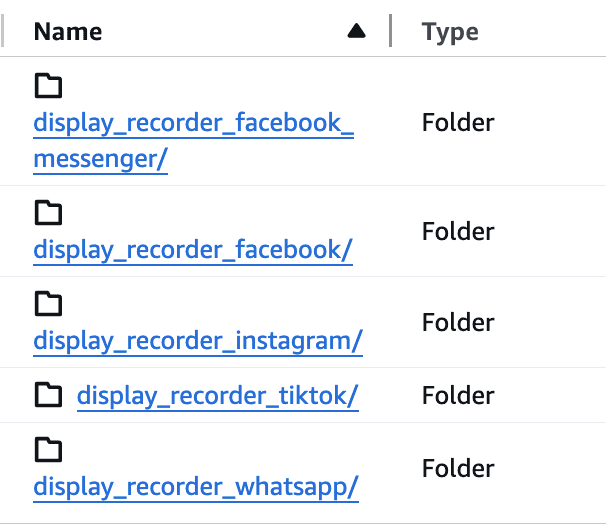
This screenshot shows how the folders of what the spyware captured appeared in the database.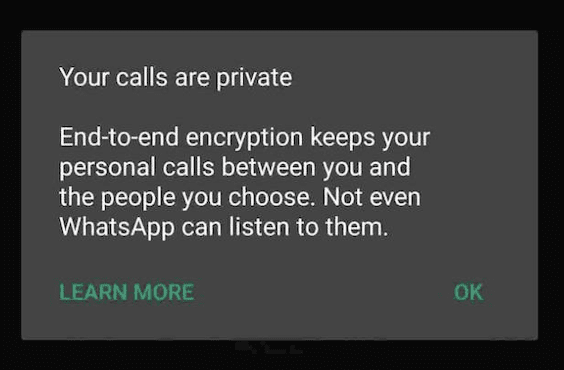
This is an actual screenshot taken from one of the images of the victim’s phone. While the chat server is secure, the device is providing a false sense of security.
Editor’s note: Encrypted chat apps like WhatsApp use end-to-end encryption, meaning only the sender and recipient can read the messages. However, encryption only protects data in transit, so once a message is displayed on a device, either participant can take screenshots or otherwise save the conversation. This means privacy can still be compromised if a device is accessed by others or if the other person chooses to capture and share the content.
What is stalkerware, and is it legal?
Stalkerware is a type of spyware that can be installed on a phone, tablet, or computer to secretly monitor another person’s activities without their knowledge or consent. Once the software is installed, it can potentially track the victim’s location, read messages, record calls, access photos, and monitor social media. Some types of spyware can even activate microphones or cameras.
Stalkerware is often marketed as harmless monitoring or tracking, but in reality, it is commonly used in unauthorized surveillance. The software operates covertly without any indications that it has been installed, and victims may not realize their private communications or physical locations are being monitored. While it is technically possible for these malicious applications to be installed remotely through deceptive techniques, it is less common, and physical access to the device is typically the most common method for a criminal to install stalkerware.
The use of stalkerware is a serious violation of privacy because it allows unauthorized individuals to access personal and private information without permission or knowledge. When stalkerware is used, the victim has not given consent, and the software might expose highly sensitive details, including passwords, private conversations, daily routines, and basically all aspects of their digital lives. This type of surveillance can lead to emotional harm, identity theft, blackmail, or even physical threats.
In many countries and regions, installing or using stalkerware without consent is illegal. Laws related to computer misuse, unauthorized access, wiretapping, and data protection often prohibit secretly monitoring someone’s device or communications. Privacy and cybersecurity laws in the European Union, the United States, Canada, and Australia classify the use of stalkerware as a criminal offense if it is installed on a device without the owner’s knowledge and permission,with harsh financial penalties and prison sentences of up to 10 years.
From a technical perspective, stalkerware is a type of spyware that is installed on a device, usually a smartphone, with the goal of silently collecting and transmitting user data to a remote server controlled by the person monitoring the device. Once installed, the software often requests elevated permissions such as access to accessibility services, device administrator privileges, or full disk access, allowing it to monitor data like text messages, call logs, GPS location, photos, and app usage. Many stalkerware applications run as background services and attempt to hide by disguising themselves as system processes or by removing their icon from the home screen.
Data collected by the software is typically transmitted over the internet to a cloud-based dashboard where the individual who installed the stalkerware can log into their account and view details like screenshots, location history, and other tracking information in near-real time. Some advanced variants also intercept notifications, capture keystrokes, record audio, or periodically take screenshots. Because the software relies on persistent permissions and background execution, it can continue operating without obvious signs to the device owner unless security tools or system audits detect the abnormal behavior.
How to know if you have spyware on your device?
Despite the software attempting to go unnoticed, some signs may indicate that the device is infected with spyware. These include unusual system behavior, battery drain, higher than regular data usage, overheating, unexpected pop-ups, or unfamiliar apps mysteriously appearing. In some cases, devices may run slower than usual, restart unexpectedly, or show strange permissions requests.
While everyday users may not have the technical expertise to analyze system logs or identify hidden software, real-world signs may suggest that someone is tracking you. If someone knows things they shouldn’t without explanation and it raises suspicions, it’s worth being cautious. If a person seems to know where you are or shows up unexpectedly, it could potentially be an indication that you are being tracked and not a harmless coincidence.
How to prevent or remove spyware and stalkerware
Preventing spyware or stalkerware infections primarily involves maintaining physical control of the device combined with good digital security practices. Using strong passwords, biometric authentication, and multi-factor authentication (MFA) are key steps in protecting your device. This makes it more difficult for someone to physically access your device and install monitoring software.
It is also important to keep operating systems and applications updated because security patches can often fix vulnerabilities that spyware might exploit. Additionally, users can enable built-in security features such as Google Play Protect or Apple’s system security protections and install security software that can help detect malicious programs.
If you suspect that stalkerware is on your device, I recommend examining the list of installed apps and removing anything that is unfamiliar or suspicious. I also suggest scanning the device using security or antivirus software to identify known spyware. In addition, check the device administrator settings and accessibility permissions because stalkerware often uses these features to gain control of the device. Finally, a full factory reset of the device can often remove hidden spyware, but in some cases, restoring from a cloud backup can reintroduce the problem if the backup includes the malicious app or compromised settings.
Once the device has been reset, only reinstall apps from official sources and change any passwords for important accounts such as email, banking, and social media. If the situation involves harassment or personal safety concerns, it may be necessary to report the incident to local authorities before removing the spyware so that it can be documented as evidence.
As part of my research into stalkerware and mobile surveillance threats, I examined real-world cases that illustrate how invasive these tools can be. In this article, I’ve referenced anonymized findings from my investigation, including examples of images captured by stalkerware that reveal the types of information it can collect. These images demonstrate how stalkerware can secretly capture screenshots of private messages, social media activity, location data, contact lists, photos, and other sensitive information directly from a victim’s device.
Although the case involves public figures such as celebrities and social media influencers, making it likely to attract media attention, the underlying issue is not limited to high-profile targets. The same tools used in these incidents are commonly deployed in broader cybercrime, harassment, and stalking situations affecting everyday users.
My goal in publishing these findings is to raise awareness about the risks posed by stalkerware while protecting the identities of those involved. By showing real examples of what this type of software can capture, readers can better understand the seriousness of the privacy violations, ways to identify and protect themselves against it, and the potential harm it can cause.
This case highlights how easily personal communications and online interactions can be monitored when malicious software is present. My intention is to highlight these cybersecurity threats and provide guidance on how to identify and mitigate similar forms of digital surveillance.
As an ethical security researcher, I do not download the data I discover. I only take a limited number of screenshots when necessary and solely for verification and documentation purposes. I do not conduct any activities beyond identifying the security vulnerability and notifying the relevant parties. I disclaim any and all liability for any and all actions that may be taken as a result of this disclosure. I publish my findings to raise awareness of issues of data security and privacy. My aim is to encourage organizations and individuals to proactively safeguard sensitive information against unauthorized access.