Expressvpn Glossary
Data integrity
What is data integrity?
Data integrity refers to the assurance of accuracy, consistency, and reliability of information throughout its lifecycle, both conceptually and in direct reference to the underlying processes that make this happen. It ensures that data remains unaltered during creation, storage, transmission, and retrieval, so that it remains trustworthy and usable.
See also: Data entry, data mining, data warehouse
How does data integrity work?
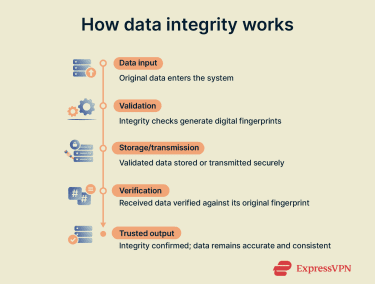 Data integrity is maintained through mechanisms that verify correctness and detect tampering throughout the information lifecycle.
Data integrity is maintained through mechanisms that verify correctness and detect tampering throughout the information lifecycle.
Examples that apply across databases, data transmission, and storage environments include:
- Checksums and cryptographic hashes, which verify that data hasn’t been altered.
- Validation rules, which enforce consistency by checking data against defined formats or constraints.
- Monitoring systems, which can detect unauthorized changes and trigger alerts or automated corrective actions.
In databases, Atomicity, Consistency, Isolation, Durability (ACID) principles ensure reliable transaction processing and data consistency. In data transmission, tools like Cyclic Redundancy Check (CRC) verify that data is received corruption-free.
Why is data integrity important?
Reliable data is the foundation of any trustworthy system. Data integrity ensures that decisions, analyses, and transactions rely on accurate information. It also helps prevent data loss, corruption, or manipulation, which can lead to financial errors, security breaches, or compliance violations.
Data integrity is vital in sectors such as finance, healthcare, and cybersecurity, where precision and accountability are mandatory. It supports compliance with regulatory frameworks like the Health Insurance Portability and Accountability Act (HIPAA) in the U.S. and the EU’s General Data Protection Regulation (GDPR).
Where is data integrity applied?
Data integrity principles extend across multiple environments, including:
- Databases: Structured query language (SQL) and not only SQL (NoSQL) systems rely on transactional rules (such as those defining how ACID principles are implemented) to maintain consistency and prevent partial or conflicting updates.
- File storage and backups: Validation tools and checksums confirm that stored files stay unaltered, ensuring data remains trustworthy during recovery or long-term retention.
- Network transmissions: Integrity checks, such as CRCs or hashes, verify that transmitted data matches the original.
- Digital signatures: Cryptographic methods confirm the authenticity and integrity of records or documents, making any unauthorized changes immediately detectable.
Benefits and limitations
It’s important to understand the advantages and challenges of data integrity. This overview highlights what it protects and its limitations.
| Benefits | Limitations |
|
|
Further reading
- SSL vs. TLS: Key differences and why TLS is better
- Zero-trust data protection explained
- What is the Internet of Things?
