-

Is Amazon safe? A complete guide for smart shopping
Amazon is one of the world’s largest online marketplaces, used daily for everything from household essentials to high-value electronics. But “safe” can mean different things depending on what yo...
-
CEO fraud: How it happens and how to protect your business
Sometimes, all it can take is one convincing message to move real money. A finance manager might get an email that looks like it came from the CEO, asking them to pay an invoice. It looks normal, the ...
-

How to spot and report an Amazon phishing email
Phishing emails pretending to be from Amazon have become so convincing that even cautious shoppers can be deceived. These messages often copy Amazon’s branding, tone, and layout and may reference re...
-
How to delete your WeChat account (complete guide)
This step-by-step guide will show you how to delete your WeChat account without hassle. We’ll also cover what you should consider before going through with the process and what happens to your data ...
-

How to spot and avoid a Publishers Clearing House scam
Publishers Clearing House (PCH) scams have become a common way for fraudsters to target unsuspecting individuals. These scams often impersonate the well-known sweepstakes company to trick people into ...
-

How to spot and avoid Etsy scams while shopping online
Etsy is an online marketplace where buyers purchase items from individual shops, including handmade, vintage, and custom products. Like other large marketplaces, Etsy also sees scams. Some listings or...
-

What is Ransomware-as-a-Service (RaaS)?
Ransomware-as-a-Service (RaaS) is a cybercrime business model in which ransomware developers create, maintain, and monetize ransomware platforms by leasing them to affiliates, who conduct intrusions a...
-
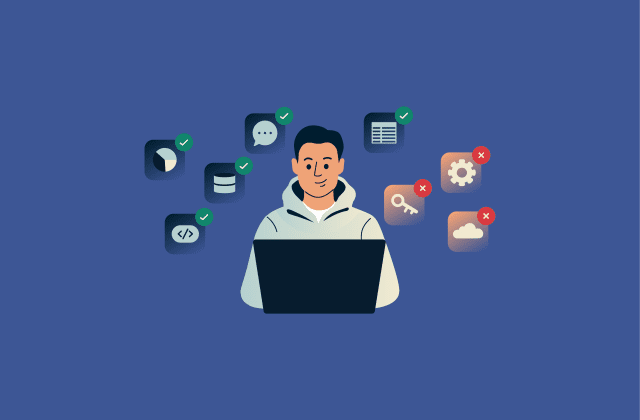
What is shadow IT, and why it matters for security
Shadow IT has become a common feature of modern workplaces as cloud services, Software-as-a-Service (SaaS) platforms, and browser-based tools make it easy for teams to adopt new technology quickly, of...
-
How to detect and prevent barrel phishing attacks
Barrel phishing attacks unfold slowly and rely on your attention, your routine, and the moments when you least expect manipulation. Even strong security tools can’t replace your own awareness, espec...
-
Avoiding Target gift card scams: What you need to know
Target gift card scams take multiple forms, from tampered gift cards secretly drained upon loading the card to fake “government agents” pressuring you to pay them via gift cards. In many cases, re...
Featured