Expressvpn Glossary
Tunneling
What is tunneling?
Tunneling is a networking technique that wraps data packets inside other packets (encapsulation) to carry them across a network. It enables unsupported protocols, connects different network types like IPv4 and IPv6, helps traffic pass through firewalls, and creates private pathways, such as virtual private networks (VPNs), while protecting data with encryption (optional).
How does tunneling work?
Tunneling takes the original data packet and wraps it inside another packet that uses a protocol the carrier network understands. This process adds a new header that tells the receiving system how to handle the enclosed data. Depending on the protocol, the encapsulated data may also be encrypted to prevent unauthorized access.
Once encapsulated, packets travel through a logical tunnel between the sender and receiver. Although the data still moves across the regular network path, the tunnel ensures it is handled consistently and protected from inspection or modification, depending on protocol. At the destination, the outer header is removed (decapsulation), revealing the original packet, which is then delivered to the correct application or system.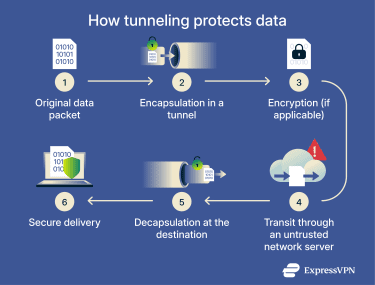
Why is tunneling important?
Tunneling allows different networks and systems to work together, making it possible to create complex network setups. Without it, organizations couldn’t link multiple office networks, and employees wouldn’t be able to access internal systems from remote locations.
Tunneling is also the foundation of VPN technology, which protects data as it travels across insecure networks. By encrypting data as it travels through the tunnel, VPNs help ensure confidentiality and integrity, meaning the information stays private and can’t be altered along the way when properly configured.
Finally, tunneling can sometimes help bypass network restrictions or censorship. Because the original data is encapsulated inside the tunnel, it can make traffic harder for some network filters or firewalls to inspect.
How tunneling impacts security and privacy
Tunneling has many benefits, but it can also open up risks. It makes it more difficult for network filters and monitoring tools to inspect data. This means malicious traffic could slip through undetected. Additionally, if tunnels are misconfigured or not carefully controlled, internal resources may be exposed to unauthorized access.
To reduce these risks, it’s important to make sure that only trusted systems can use a tunnel. This can be accomplished by implementing strong authentication, which helps ensure that the devices at each end are who they claim to be. Endpoint validation provides an additional layer of protection by verifying that the tunnel endpoints meet expected security or configuration requirements. Choosing a reputable, audited tunneling protocol further lowers risk, as not all tunneling methods provide the same level of security.
Popular tunneling protocols and how they’re used
There are several tunneling protocols commonly used today, each designed for specific purposes. Here are some of the most popular ones:
- OpenVPN: A tried-and-tested VPN tunneling protocol, it’s highly configurable and compatible with a wide range of platforms, making it popular for both businesses to secure remote access and individuals to browse privately.
- Secure Shell (SSH): It’s mainly used to provide encrypted connections for individual apps or specific services. Administrators use it for remote management, secure file transfers, or forwarding application traffic over an encrypted tunnel.
- Internet Protocol Security (IPsec): It provides encrypted connections at the network level. IPsec is frequently used for secure data transport between office networks via site-to-site VPNs.
- Generic Routing Encapsulation (GRE): It's flexible, lightweight, and widely supported, but it doesn’t encrypt data. GRE is often used when multiple types of traffic, like IPv4, IPv6, or multicast, need to travel together over a network.
- WireGuard: A modern, lightweight VPN protocol with a minimal codebase. Its lean design enables fast connections for browsing and remote access.
Further reading
- What is a VPN tunnel
- What is VPN split tunneling
- Split tunneling vs. full tunneling: Which should you use?
