Expressvpn Glossary
Security operations center (SOC)
What is a security operations center?
A security operations center (SOC) is a centralized unit that monitors and maintains an organization’s security posture. It brings together the people, processes, and technology responsible for detecting and responding to cyber incidents. It watches for unusual activity, investigates potential threats, and takes action to protect data and systems before issues escalate.
Core functions of a SOC
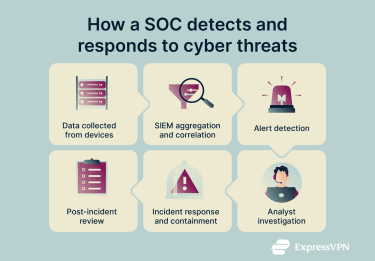
A SOC works through a repeatable cycle to detect and respond to threats. Each stage in the process builds on the last to keep the network secure.
- Data collection: The SOC gathers logs and telemetry from servers, endpoints, and other devices to build a complete picture of what is happening on the network.
- Security information and event management (SIEM) aggregation and correlation: This data flows into a SIEM platform, where it’s organized, analyzed, and compared to known patterns or indicators of compromise.
- Alert detection: When the SIEM spots unusual activity, it generates alerts that help the team focus on the events that need attention.
- Analyst investigation: SOC analysts review each alert, validate whether it represents a real threat, and decide what action to take.
- Incident response and containment: If the alert is confirmed, the team works to contain the threat quickly, limit damage, and restore normal operations.
- Post-incident review: After the incident, the SOC reviews what happened, identifies root causes, and updates defenses to prevent similar issues in the future.
SOC structure and key roles
A SOC relies on a hierarchy of professionals, each with specific responsibilities. A SOC analyst is the most common role, but the team includes several levels:
- Chief Information Security Officer (CISO): Oversees the organization’s overall security strategy and typically provides executive oversight for the SOC.
- SOC manager: Runs the SOC’s day-to-day operations, including team management, budgeting, and internal processes.
- Incident response lead: Coordinates the response to major incidents and leads advanced response efforts during high-severity events.
- SOC engineer: Builds and maintains the SOC’s tools, pipelines, and internal systems.
- Tier 1 analyst: Handles initial alert triage. They review incoming data to determine if a threat is real or a false alarm.
- Tier 2 analyst: Manages in-depth investigation. If a Tier 1 analyst confirms a threat, the Tier 2 analyst looks for the scope of the breach and coordinates the response.
- Tier 3 analyst: Conducts advanced forensics and malware analysis. They handle the most severe incidents and look for hidden threats.
- Threat hunter: Proactively searches networks for threats that automated systems might have missed.
Tools and technologies used in SOCs
Teams rely on specialized SOC tools to process the vast amount of data generated by modern networks. These include:
- SIEM: These platforms collect and aggregate log data from across the organization to identify patterns and potential threats.
- Security orchestration, automation, and response (SOAR): These systems automate routine tasks and help coordinate incident response.
- Endpoint detection and response (EDR): These tools monitor individual devices (endpoints) for suspicious behavior.
- Threat intelligence feeds: These sources provide external information about known threats, malicious actors, and attack techniques.
- Vulnerability management platforms: These tools scan systems to find weaknesses that need patching.
SOC vs. network operations center (NOC)
While they often work closely together, the difference between SOC and NOC lies in their primary objectives:
| Feature | SOC | NOC |
| Focus | Security and threat mitigation | Network performance and uptime |
| Objective | Protect data and systems from malicious actors | Keep the network running fast and without interruption |
| Staff skills | Cybersecurity, forensics, and threat analysis | Networking, engineering, and system optimization |
Why security operations centers are important
A SOC provides constant visibility into network activity, helping teams detect threats early and limit damage through rapid incident response. It also supports compliance with data laws and builds trust with partners. By functioning as a central intelligence hub, a SOC strengthens defense and awareness throughout the organization.
Best practices for SOC effectiveness
A SOC must stay ahead of attackers using best practices:
- Task automation: Using SOAR tools to handle routine alerts, leaving analysts free to focus on difficult problems.
- Playbook use: Having clear, written procedures for common types of incidents.
- Updated rules: Frequently adjusting detection rules and threat feeds to match the current threat environment.
- Defense testing: Running regular simulations to find gaps in the defense.
- Secure communications: Using encryption and virtual private networks (VPNs) to protect SOC communications and data in transit.
Common challenges SOC teams face
Despite their value, SOCs face significant hurdles:
- Alert fatigue: Analysts receive too many notifications and sometimes false alarms, leading them to miss real threats.
- Staff shortages: There is a global lack of skilled cybersecurity professionals.
- New threats: Attackers constantly change their methods, requiring the SOC to adapt quickly.
- Legacy systems: Integrating old hardware and software with modern security platforms is often difficult.
Further reading
- What is OPSEC, and why do you need it?
- The 7 pillars of zero-trust security
- Guide to combat digital stalking and harassment
