Expressvpn Glossary
Playfair cipher
What is the Playfair cipher?
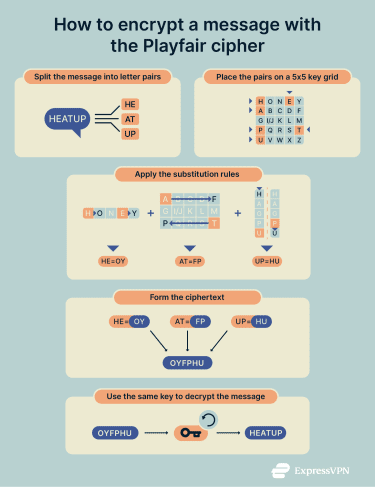
The Playfair cipher is a manual encryption method that protects messages by encrypting pairs of letters instead of single characters. It uses a 5×5 grid that contains all letters of the alphabet, with I and J usually sharing one space to fit the grid.
How does the Playfair cipher work?
The Playfair cipher starts by building a 5×5 key square using a chosen keyword. This square determines how each pair of letters in a message is substituted. Once the key square is set, the plaintext is split into pairs, adjusted for repeated letters, and then transformed based on their positions in the grid.
- Key square creation: The key square is created by selecting a keyword. This step defines the layout of the 5×5 grid. The keyword is placed in the first row, keeping only the first occurrence of each letter. In this example, the keyword is “HONEY.” The remaining spaces are then filled with the unused letters of the alphabet in order, with I and J combined into a single cell.
- Plaintext preparation: The plaintext is prepared by dividing the message into pairs of letters. If a pair contains the same letter, a filler such as X is inserted between them (for example, MEET becomes ME, EX, ET). In this example, the word “HEATUP” becomes HE, AT, UP. These pairs are then encrypted using the Playfair rules in the next step.
| H | O | N | E | Y |
| A | B | C | D | F |
| G | I/J | K | L | M |
| P | Q | R | S | T |
| U | V | W | X | Z |
- Substitution rule application: Each letter pair is located in the key square and substituted according to the Playfair rules. The grid doesn’t change during this process; the rules only determine which letters replace the originals.
- Same row (H E): Both letters are in the first row, so each one is replaced by the letter immediately to its right (wrapping to the start of the row if needed).
H → O, E → Y.
- Rectangle rule (A T): A and T form the corners of a rectangle. Each letter is replaced by the letter in the same row but in the other letter’s column.
A → F, T → P.
- Same column (P U): Both letters are in the first column, so each one is replaced by the letter directly below it (wrapping to the top of the column if needed).
U → H, P → U.
- Ciphertext formation: The substituted pairs produce the final encrypted text. Decryption follows the same process in reverse. In this example, the plaintext HEATUP becomes OYFPHU.
Why is the Playfair cipher important?
The Playfair cipher was the first method to use polygraphic substitution. This technique encrypts pairs of letters, making basic frequency analysis less effective. It demonstrated an early step forward in manual encryption at a time when most ciphers operated on single characters.
It was also used for military communication in the early 20th century because it offered stronger protection than earlier hand-operated systems. The ideas behind it helped form the basis for modern symmetric encryption methods, showing how classical techniques evolved into the structured algorithms used today.
Security and privacy considerations
The Playfair cipher is historically significant but not secure by modern standards.
- Weak security: Messages can be deciphered easily using frequency analysis and pattern detection on digraphs.
- Modern relevance: The cipher helped cryptography evolve from manual systems to digital encryption methods such as Advanced Encryption Standard (AES) and Rivest–Shamir–Adleman (RSA).
- Educational value: Instructors use it to demonstrate fundamental concepts in cryptography and cybersecurity education.
Playfair cipher vs. modern encryption
The Playfair cipher is a manual, letter-based system that relies on a shared keyword and simple substitution rules. Modern encryption methods operate on digital data using mathematically complex algorithms designed to protect information at scale.
| Playfair cipher | Modern encryption | |
| Type | Manual, paper-based | Digital, algorithmic |
| Method | Letter pair substitution | Bit-level computation |
| Key | Shared keyword | Long binary key |
| Security | Easily broken | Cryptographically strong |
| Use | Historical, educational | Active digital protection |
This shift from grid-based substitution to algorithmic processing reflects the transition from classical cryptography to the computational encryption techniques used today.
Further reading
- What is the Caesar cipher? Definition, history, and examples
- What is cryptography?
- The history of encryption: From ancient codes to digital security
