Expressvpn Glossary
Network access control (NAC)
What is network access control?
Network access control (NAC) is a security control that manages which users and devices can connect to a network, under what conditions, and with what level of access. It authenticates the user, checks the device’s identity and security posture against defined policies, and then grants, restricts, or blocks access.
The purpose of NAC is to ensure that only trusted, compliant users and devices can reach sensitive network resources.
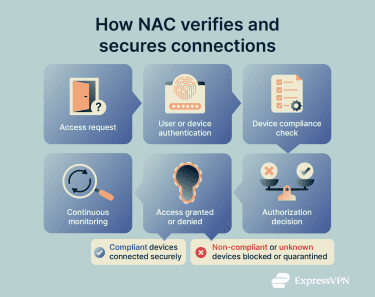
How does network access control work?
NAC acts as a gatekeeper for network access. It evaluates each connection attempt before allowing a device to communicate with network resources.
Typical NAC workflow:
- Connection attempt: A device tries to join the network, and its traffic is directed to the NAC system.
- Identity verification: NAC authenticates the user or identifies the device, often using credentials, certificates, or directory services.
- Posture and compliance check: NAC evaluates whether the device meets defined security requirements, such as current patches, enabled encryption, and active security software.
- Policy decision: NAC compares the connection and posture information against configured policies to determine the appropriate level of access.
- Access enforcement: The network applies the decision, granting full access, placing the device in a restricted segment, or blocking it from connecting.
- Continuous monitoring: NAC monitors the session and can change or revoke access if the device posture or behavior falls out of compliance.
Types of network access control
- Pre-admission NAC: Enforces access policies before a device is allowed onto the network, checking identity and security posture first.
- Post-admission NAC: Applies controls after a device has connected, monitoring behavior and configuration over time and adjusting or revoking access if it falls out of compliance.
- Agent-based NAC: Uses a software agent on the device to report detailed security and configuration information to the NAC system for fine-grained enforcement.
- Agentless NAC: Performs checks without installing software on devices, relying on network activity, protocols, and device profiling; commonly used for Internet of Things (IoT), guest, and unmanaged devices.
Why is NAC important?
NAC strengthens network security by enforcing consistent access policies and controlling which users and devices can reach sensitive resources.
- Limits unsafe and unauthorized access: Blocks unknown or non-compliant devices from connecting to internal networks.
- Supports threat containment: Restricts or quarantines devices that show signs of malware, misconfiguration, or risky behavior.
- Enforces least-privilege and zero-trust strategies: Assigns access based on identity, role, and device posture, aligning with least-privilege and zero-trust models.
- Aids compliance: Helps meet regulations, such as the Health Insurance Portability and Accountability Act (HIPAA) and the General Data Protection Regulation (GDPR), by controlling access to sensitive systems and providing logs for audits.
- Improves visibility: Builds a unified inventory of connected devices, including unmanaged and IoT endpoints, making it easier to track risk.
Common NAC solutions and tools
Organizations typically use NAC platforms that integrate with identity systems, directory services, and network infrastructure. These tools often include device profiling, automated policy enforcement, and dashboards for monitoring connected endpoints.
Many solutions also support integrations with mobile device management (MDM), endpoint security tools, and network switches or access points.
Common challenges
The effectiveness of NAC depends on how well it fits existing infrastructure. Typical challenges include:
- Legacy systems: Older or unmanaged devices may not support consistent security checks.
- Balancing usability with strong controls: Strong verification can introduce delays or disrupt workflows.
- Scaling across hybrid and distributed networks: Keeping policies consistent across offices, cloud, and remote access is complex.
- Updating policies in real time: Updates must be applied quickly without breaking active connections.
Further reading
- Network connections: Everything you need to know
- Zero-trust network access (ZTNA) explained
- Network architecture: Building secure and modern networks
