Expressvpn Glossary
Ring network
What is a ring network?
A ring network is a network topology in which each device (node) connects to exactly two neighboring nodes in a closed loop with no central hub or switch directing traffic. Data travels from node to node until it reaches its destination.
How does a ring network work?
In a standard ring network topology, data moves in a unidirectional flow (one way). When a device transmits data, the packet enters the ring and passes through each node in sequence. Each node checks the destination address. If the packet is addressed to that node, it copies and processes the data; if not, it forwards the packet to the next node.
Many ring implementations use token passing (Token Ring). A control packet (the token) travels around the ring continuously. Only the node holding the token can transmit data. This method prevents collisions and ensures each device has equal access to the network. After transmission, the token is released and continues around the ring.
Dual ring networks add redundancy by running two counter-rotating rings. If a link or device fails on one path, traffic automatically reroutes to the other ring, maintaining network operation.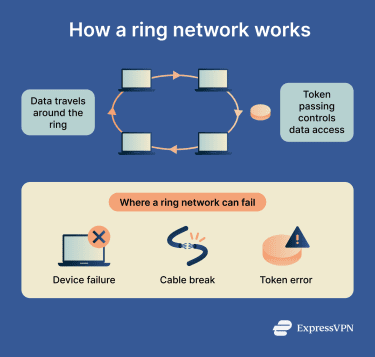
Why are ring networks important?
Ring networks offer high performance under heavy traffic with no data collisions due to orderly, unidirectional token passing, ensuring equal access for all devices. They are easy to install, cost-effective, and provide reliable, consistent performance without needing a central server.
Dual-ring setups add resilience, allowing data to be rerouted in the opposite direction if a link fails. And because each device connects to only two others, isolating faults, such as a broken cable or malfunctioning node, is straightforward.
Where are ring networks used?
Ring networks are common in scenarios that require high reliability.
- Telecommunications networks: Ring structures are widely used in fiber-optic networks to provide a reliable, high-speed backbone for voice and data traffic, allowing for quick rerouting if a connection fails.
- Industrial automation and control systems: They are used to connect sensors, programmable logic controllers, and machinery in factories that require consistent, real-time data exchange.
- Metropolitan area networks (MANs): Fiber-based ring topology connects different local area networks (LANs) across a city.
- Utility and transportation networks: Used for controlling traffic lights, railway communications, and in power utility systems where high reliability is necessary.
- Legacy LANs: Historically, token ring networks were used in offices for local data transmissions.
Risks and privacy concerns
While ring networks are efficient for traffic, their dependence on every node acting as a repeater introduces specific operational and security risks.
- Single point of failure: In a traditional unidirectional ring, if one node or cable fails, the entire network fails.
- Token manipulation: Attackers can inject malformed tokens or steal the token used in token passing, leading to network paralysis or unauthorized data access.
- Limited scalability: Adding or removing devices disrupts the network, requiring downtime.
- High latency: Data may have to pass through numerous nodes to reach its destination, increasing transmission time.
Further reading
- Network topology: Best practices for modern networks
- Network mapping: A complete guide
- What is computer networking and how VPNs fit in
- Network connections: Everything you need to know
- What is routing, and why does it matter in networking?

