Expressvpn Glossary
DNS sinkhole
What is a DNS sinkhole?
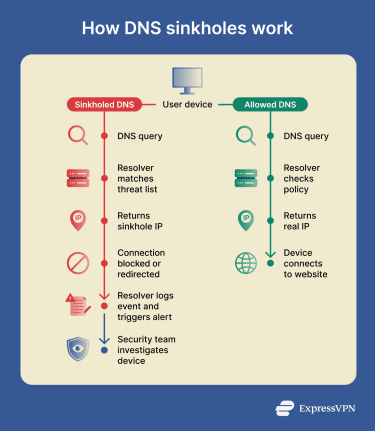
A Domain Name System (DNS) sinkhole (also called a DNS blackhole) is a cybersecurity mechanism that intercepts DNS requests for known malicious domains and returns a false, controlled IP address instead of the actual destination. This “blackholes” traffic and prevents devices from connecting to harmful sites while allowing security teams to identify infected, botnet-compromised machines.
How does a DNS sinkhole work?
A DNS sinkhole intercepts DNS requests and alters the response for malicious domains.
- DNS query intercepted: When a user or device tries to connect to a known malicious domain (evaluated against a feed of known threat data), the DNS server (configured as a sinkhole) detects the query.
- DNS response rewritten: The DNS server replies with a predefined false IP address instead of the actual IP.
- Connection redirected: The connection to the malicious domain fails because the traffic is directed to a non-existent or, in some cases, a monitoring (honeypot) server.
- Event recorded: Security professionals monitor logs for traffic aimed at the sinkhole IP, allowing them to pinpoint which devices within the network are infected with malware or attempting to connect to forbidden sites.
Types of DNS sinkholes
- DNS server-based sinkhole: Uses software to maintain blocklists of malicious domains and responds to queries for these domains with a non-routable IP address.
- Local/firewall-based sinkhole: Usually used on a next-generation firewall or appliance. This method identifies malicious traffic and replaces the legitimate IP with a sinkhole to identify compromised internal hosts.
- Cloud-based DNS sinkhole: Offered by security vendors as a managed service to provide real-time threat intelligence and filtering.
- Internet service provider (ISP)-level sinkhole: Internet service providers may deploy sinkholes to disrupt access to known malicious domains or as a tool for enforcing internet censorship.
Why are DNS sinkholes important?
DNS sinkholes help reduce the exposure to threats that rely on domain names by preventing devices from reaching known phishing sites and malware distribution domains. When a request is redirected to a sinkhole instead of the real destination, infected systems can’t communicate with malicious servers, including botnet command-and-control infrastructure.
Sinkhole logs can also help identify compromised devices. Queries redirected to a sinkhole are recorded and analyzed, allowing security teams to detect hosts attempting to contact malicious domains.
Risks and privacy concerns
DNS sinkholes inspect and may log DNS queries, which introduces privacy considerations:
- DNS query data can be sensitive: Domain names queried can reveal which services or sites a device is trying to reach.
- Resolvers can observe DNS traffic: Central resolvers (DNS servers that translate domain names to IP addresses) can see large volumes of DNS requests within an environment.
- Encrypted DNS affects visibility: DNS over HTTPS (DoH) and DNS over TLS (DoT) can reduce local resolver visibility if queries are sent to external resolvers.
- Logging creates retention and access requirements: Stored DNS logs may require controls for access, retention periods, and secure storage.
| DNS works well for | DNS does not cover |
| Blocking known malicious domains listed in policy lists or threat feeds | New or unknown malicious domains not yet listed |
| Preventing infected devices from reaching the command-and-control infrastructure | Threats that connect directly to IP addresses without performing a DNS lookup |
| Network-wide enforcement through centralized DNS controls, without installing agents on devices | DNS queries sent through external resolvers using encrypted DNS protocols such as DoH or DoT |
| Logging suspicious domain requests, which can help identify potentially compromised devices | Malware removal or remediation on infected devices |
DNS sinkholes help reduce exposure to known malicious domains and support early detection of suspicious activity but are not a standalone security solution and should be combined with other security controls.
Further reading
- What is DNS spoofing? Learn how it affects your security
- DNS hijacking and how to prevent it
- What is a DNS leak? How to check, fix, and prevent it
- The ultimate guide to recursive DNS: Everything you need to know
- What is DNS, and how does it work?

