Expressvpn Glossary
DNS attack
What is a DNS attack?
A DNS attack is a cyberattack targeting the Domain Name System (DNS), the system that translates domain names into IP addresses that computers use to locate each other. DNS attacks aim to disrupt or manipulate this process, which can result in websites becoming slow or unavailable or users being redirected to malicious sites.
How does a DNS attack work?
When a domain name gets typed into a browser, the device’s stub resolver sends a query to a recursive resolver (often operated by the internet service provider (ISP) or a public DNS provider). If the resolver doesn’t already have the answer cached, it queries the DNS hierarchy (contacting root servers, top-level domain (TLD) servers, and finally the domain’s authoritative name server) to retrieve the correct IP address.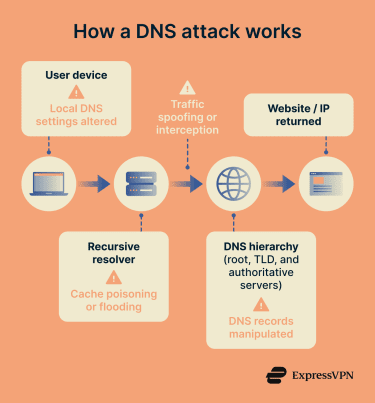
When DNS was developed in the 1980s, security wasn’t a priority, and it was designed without built-in authentication or encryption. This means attackers can target multiple points in the resolution chain:
- The user’s device (by altering local DNS settings).
- The recursive resolver (by poisoning its cache or overwhelming it).
- The communication channel between servers (via spoofing or interception).
- The authoritative name server itself.
By interfering, attackers can redirect users to malicious websites, intercept data, or disrupt access to legitimate services.
Types of DNS attacks
Some common types of DNS attacks include:
- DNS tunneling: Exploits the DNS protocol by transporting non-DNS traffic through DNS queries, allowing hackers to pass malware or sensitive data through security mechanisms like firewalls.
- DNS hijacking: Redirects users from legitimate sites to fraudulent ones by manipulating the DNS resolution process itself.
- DNS amplification: A distributed denial-of-service (DDoS) technique where attackers send small DNS queries with a spoofed source IP pointing to the victim, causing open DNS resolvers to send large responses to the target to overwhelm them with traffic.
- DNS cache poisoning: Also known as DNS spoofing, it involves entering incorrect information into DNS caches, leading to traffic being redirected to the wrong websites until the cache is refreshed.
Why are DNS attacks significant?
DNS attacks are significant because the DNS is a fundamental part of the internet, and any disruption to it can have widespread implications. For instance, the 2016 attacks on Dyn, a major managed DNS provider, led to many massive platforms, like PayPal, PlayStation Network, Amazon, and more, being down for several hours.
Beyond downtime, DNS attacks can cause malware infections or the loss of sensitive data by redirecting users to malicious websites.
Further reading
- DNS security: How to protect your network from DNS threats
- DoQ: Everything you need to know about the new DNS protocol
- What is DNS cache poisoning? How to detect and prevent attacks
- What is a DNS flood attack? Understanding its impact
- What is DNS spoofing? Learn how it affects your security
- DNS hijacking and how to prevent it

