Expressvpn Glossary
Datagram
What is a datagram?
A datagram is a self-contained unit of data sent across a network. It includes a header with addressing information and a payload containing the actual data. Routers use the header to determine where to forward it next.
Unlike connection-oriented protocols, datagrams are sent without establishing a connection first. They follow a best-effort delivery model, meaning the network tries to deliver them but does not guarantee arrival.
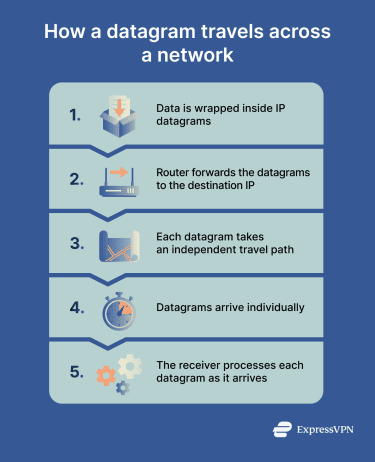
How does a datagram work?
When data is sent using a datagram-based model, it follows these steps:
- Encapsulation: Data is packaged into a transport-layer message, such as User Datagram Protocol (UDP), then wrapped in an Internet Protocol (IP) datagram with source and destination addresses and control data like time to live (TTL).
- Routing: Routers read the destination IP address and forward the datagram using their routing tables, without tracking other messages.
- Independent paths: Each datagram may take a different route depending on network conditions.
- Variable arrival: Datagrams can arrive out of order, be delayed, duplicated, or not arrive at all.
- Handling at the receiver: The receiving system processes each datagram as it arrives. Any reordering or retransmission is handled by the application or higher-level protocols.
Types of datagrams
Datagrams are used in different ways. Common types include:
- IP datagram: The basic unit used for routing data across IP networks, regardless of the content.
- UDP datagram: Operates at the transport layer, adding port numbers and basic control information before passing data to IP.
- Fragmented datagrams: Large datagrams are split into smaller pieces to fit network limits, then reassembled at the destination.
- Multicast datagrams: Sent from one source to multiple recipients at the same time, reducing the need for duplicate transmissions.
Why is a datagram important?
Datagrams offer several advantages:
- Supports fast, scalable networking: Routers don’t track connections, which reduces overhead and allows networks to scale efficiently.
- Enables real-time communication: Low latency makes datagrams suitable for time-sensitive applications where speed matters more than guaranteed delivery.
- Adapts to changing networks: Each datagram can take a different path, helping avoid congestion or failures.
- Allows flexible reliability: Higher-level protocols can add features like error correction or encryption as needed.
Where are datagrams used?
Datagrams are used across many core internet services, including:
- UDP-based services: Used for speed-sensitive tasks such as Domain Name System (DNS) queries, Voice over IP (VoIP), and some streaming technologies.
- Modern web protocols: Protocols like Quick UDP Internet Connections (QUIC), which powers HTTP/3, rely on datagrams for improved performance.
- Online gaming and live collaboration: Real-time applications such as multiplayer games and video conferencing use datagrams to reduce delays, even if some data is lost.
- Routing and control protocols: Network updates and diagnostic tools use datagrams to exchange small, time-sensitive information.
- Virtual private network (VPN) tunnels: Some VPNs encapsulate IP datagrams to transmit data securely across networks.
Risks and privacy concerns
The design of datagrams introduces certain security and privacy considerations, including:
- Unencrypted datagrams on shared networks: Standard IP and UDP datagrams don’t include encryption by default. On shared Wi-Fi networks, other users can potentially capture and read datagram contents using packet sniffing tools.
- Metadata exposure: Datagram headers contain metadata that can reveal communication patterns.
- Source spoofing and reflection: Because IP datagrams don’t verify the authenticity of the source address, attackers can perform IP spoofing. In some cases, this can be used in reflection or amplification attacks, where traffic is redirected toward a target.
- Fragmentation and filtering challenges: Attackers may exploit fragmentation techniques to evade certain firewalls, particularly if the firewalls don’t properly reassemble fragments before inspection.
Further reading
- TCP vs. UDP: Understanding the key differences and best use cases
- What is HTTP/2 and how does it work?
- What is packet loss? Everything you need to know
- What is Internet Control Message Protocol (ICMP)?
- What is traceroute and how to use it for network diagnostics

